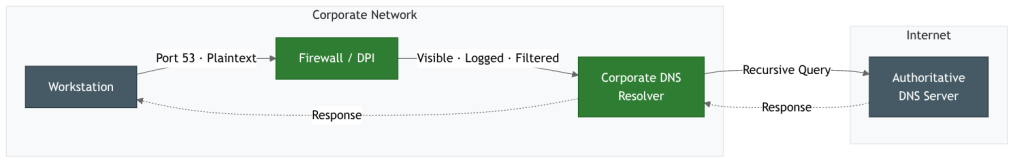
For decades, enterprise security relied on a simple truth: if you control Port 53, you can see where your users are going. Every DNS query left the network in plaintext, straightforward to log, filter, and block. DNS over HTTPS (DoH), standardized in RFC 8484 [2], broke that model by wrapping name resolution inside standard HTTPS traffic on port 443. Since the standard was published in 2018, DoH has moved from an experimental browser feature to a default setting in major browsers and a natively supported capability in most operating systems.
For privacy, this is a real improvement, especially for remote workers on untrusted networks. For corporate IT administrators, it means the DNS-based monitoring and filtering you rely on for security no longer works the way it used to.
DoH keeps the exact same DNS wire format but secures it using TLS and HTTP for transport [2]. The result is that DoH traffic gets the same protection as any other HTTPS connection. The RFC recommends HTTP/2 as a minimum to avoid performance hits, which also allows DoH to benefit from newer protocol improvements like HTTP/3.
In practice, a DoH client encodes the DNS message as application/dns-message and sends it via an HTTP GET or POST request. To simplify integration for web-based applications, providers like Google [3] and Cloudflare [4] additionally offer a JSON API.
Querying Cloudflare’s DoH resolver for www.hdm-stuttgart.de using their JSON API looks like this:
$ curl -s -H 'accept: application/dns-json' \
'https://cloudflare-dns.com/dns-query?name=www.hdm-stuttgart.de&type=A'
{
"Status": 0,
"TC": false,
"RD": true,
"RA": true,
"AD": false,
"CD": false,
"Question": [
{
"name": "www.hdm-stuttgart.de",
"type": 1
}
],
"Answer": [
{
"name": "www.hdm-stuttgart.de",
"type": 1,
"TTL": 3600,
"data": "212.132.79.37"
}
]
}This gets you the exact same result as resolving it locally over traditional DNS, just much more securely:
$ dig +noedns www.hdm-stuttgart.de A
; <<>> DiG 9.20.19 <<>> +noedns www.hdm-stuttgart.de A
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 54911
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 0
;; QUESTION SECTION:
;www.hdm-stuttgart.de. IN A
;; ANSWER SECTION:
www.hdm-stuttgart.de. 325 IN A 212.132.79.37
;; Query time: 18 msec
;; SERVER: 127.0.0.53#53(127.0.0.53) (UDP)
;; WHEN: Thu Feb 26 18:27:07 CET 2026
;; MSG SIZE rcvd: 54One of the early hurdles for DoH was figuring out how a client actually discovers an encrypted resolver over an initially unencrypted channel. RFC 9463 [5] solved this by allowing networks to advertise their designated encrypted resolvers via DHCP and Router Advertisements.
Today, adoption is widespread, and much of it is happening without your IT departments involvement. Firefox enables it by default in several regions using Cloudflare, and Firefox for Android (v143) added it as an opt-in feature recently [6]. Chrome auto-upgrades DNS queries if it detects your system resolver supports DoH.
On the OS side, Windows 11 has native DoH support, and Windows Server 2025 just introduced DoH for the DNS Server role in its February 2026 cumulative update (currently in preview) [7]. Apple supports it via MDM profiles, Android has been handling DNS over HTTP/3 via Mainline module updates since 2022 [8], and on Linux, encrypted DNS is available through systemd-resolved and tools like dnscrypt-proxy.
While alternatives like DNS over QUIC (DoQ) [9] exist, the industry has largely settled on DoH over HTTP/3. Encrypted Client Hello (ECH) [10][11] further reduces what network tools can observe by hiding SNI metadata.
For corporate IT infrastructure, DoH offers some serious security upgrades. TLS encryption stops rogue access points, compromised network segments, or ISPs from observing or modifying DNS queries. When paired with DNSSEC, you get both data authenticity and transport confidentiality.
It also stops intermediary networks from interfering with DNS routing. Because DoH runs over port 443, it is very difficult for networks to hijack DNS queries to force suboptimal datacenters. Organizations can finally pick a resolver based purely on policy and performance.
Recent standards have closed the remaining gaps: networks can now advertise their encrypted resolvers via DHCP [5], and split-horizon environments can establish local DNS authority without breaking encryption [12]. This means enterprises can route internal queries to local servers and external queries to a protective DNS provider. Running an corporate DoH resolver hooked into threat intelligence allows you to block connections to malicious domains before they establish. The NSA now positions DNS as an active threat detection layer, not just a background utility [13].
But..
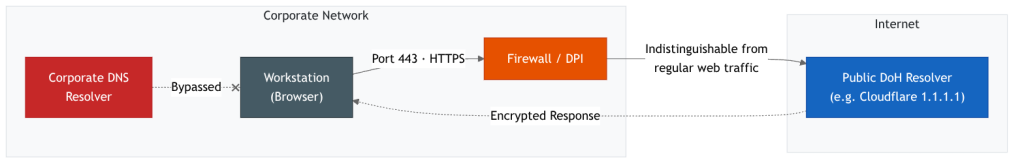
The exact properties that make DoH great for privacy, create significant challenges for enterprise monitoring. Traditional security tools rely on seeing plaintext traffic on port 53. If applications bypass the local/company DNS to use external DoH resolvers, IT entirely loses visibility.
Browsers are a primary driver of this bypass. Firefox checks for a canary domain (use-application-dns.net) at startup, if it doesn’t return NXDOMAIN, Firefox will use DoH by default in several regions [14]. This is an opt-out mechanism that requires active configuration. Chrome’s behavior operates independently of your corporate DNS unless explicitly overridden by policy.
This also creates a practical operational problem. If a browser resolves through a public DoH provider, it cannot reach internal corporate hostnames like intranet.company.local. The result may be confusing helpdesk tickets where internal sites stop working for some users but not others, depending entirely on their browser’s DNS configuration.
Despite encryption, DoH traffic isn’t completely invisible. Research shows 95% accuracy in website fingerprinting using just the first 50 DoH packets [15], consistent with earlier research [16]. DoH raises the cost of passive surveillance, but it doesn’t eliminate it.1
Malware authors have also recognized this opportunity. Threat actors now use DoH for covert command-and-control (C2) and data exfiltration. In 2024, the state-linked ShadowPad backdoor was caught using encrypted DNS tunneling [17]. The 2025 Infoblox threat report documents a broader trend of malware adopting encrypted DNS [18]. If your network tools can’t inspect DoH, these channels are invisible.
Market consolidation is another concern. Most public DoH traffic goes straight to Cloudflare and Google. While protocols like Oblivious DoH (ODoH) and Oblivious HTTP (OHTTP) have been created to separate client identity from the resolver, they aren’t widely deployed yet.
DNS is a legacy protocol that cannot be replaced overnight, but DoH is a highly effective way to modernize it without altering the underlying framework. Since 2018, it has evolved from an experiment into a core OS capability.
The trade-off is straightforward: you gain transport security but lose the plaintext visibility you had on Port 53. Waiting is not an option, your browsers are already making DoH requests whether you configured them to or not. The first step is taking control of your DNS layer. Set up DNS middleware like Unbound or CoreDNS as DoH frontends (or use the upcoming Windows Server 2025 capabilities [7]) and hook it into threat intelligence feeds to block known malicious domains before connections establish.
At the network edge, you need to block outbound connections to known public DoH resolver IPs. If you don’t push the use-application-dns.net canary domain to your network, Firefox will route your users’ DNS queries to Cloudflare without asking [14]. Once these blocks are in place, any remaining DoH traffic on your network becomes a high-fidelity signal for intentional evasion or active malware [19].
Endpoint management is also important. Browsers can be locked down via Group Policy (Chrome’s DnsOverHttpsMode policy, for example) or MDM profiles to force the use of internal resolvers. For deeper OS-level control, Microsoft’s Zero Trust DNS (ZTDNS) [20] ensures all resolution goes through designated encrypted resolvers; administrators configure protective servers using netsh dnsclient add ztdns and can block all other outbound DNS [21].
DNS is no longer a passive utility. With DoH becoming the default, you either manage your DNS layer actively or lose visibility into it entirely.
- These figures come from controlled lab environments. Real-world accuracy is lower due to caching and concurrent connections. ↩︎
References
[1] P. V. Mockapetris, “Domain names – implementation and specification,” Internet Engineering Task Force, Request for Comments RFC 1035, Nov. 1987. doi: 10.17487/RFC1035.
[2] P. E. Hoffman and P. McManus, “DNS Queries over HTTPS (DoH),” Internet Engineering Task Force, Request for Comments RFC 8484, Oct. 2018. doi: 10.17487/RFC8484.
[3] “Make API requests to 1.1.1.1 over DoH,” Cloudflare Developers. [Online]. Available: https://developers.cloudflare.com/1.1.1.1/encryption/dns-over-https/make-api-requests/
[4] “JSON API for DNS over HTTPS (DoH),” Google Developers. [Online]. Available: https://developers.google.com/speed/public-dns/docs/doh/json
[5] M. Boucadair, T. Reddy.K, D. Wing, N. Cook, and T. Jensen, “DHCP and Router Advertisement Options for the Discovery of Network-designated Resolvers (DNR),” Internet Engineering Task Force, Request for Comments RFC 9463, Nov. 2023.
[6] “Firefox for Android 143.0 Release Notes,” Mozilla, Sep. 2025. [Online]. Available: https://www.firefox.com/en-US/firefox/android/143.0/releasenotes/
[7] “Secure DNS with DoH: Public Preview for Windows DNS Server,” Microsoft Tech Community, 2026. [Online]. Available: https://techcommunity.microsoft.com/blog/networkingblog/secure-dns-with-doh-public-preview-for-windows-dns-server/4493935
[8] “DNS over HTTP/3 in Android,” Google Security Blog, Jul. 2022. [Online]. Available: https://security.googleblog.com/2022/07/dns-over-http3-in-android.html
[9] C. Huitema, S. Dickinson, and A. Mankin, “DNS over Dedicated QUIC Connections,” Internet Engineering Task Force, Request for Comments RFC 9250, May 2022.
[10] E. Rescorla et al., “TLS Encrypted Client Hello,” Internet Engineering Task Force, Internet-Draft draft-ietf-tls-esni-25, 2025. [Online]. Available: https://datatracker.ietf.org/doc/html/draft-ietf-tls-esni-25
[11] “Announcing Encrypted Client Hello,” The Cloudflare Blog. [Online]. Available: https://blog.cloudflare.com/announcing-encrypted-client-hello/
[12] T. Pauly et al., “Establishing Local DNS Authority in Validated Split-Horizon Environments,” Internet Engineering Task Force, Request for Comments RFC 9704, Jan. 2025.
[13] “Adopting Encrypted DNS in Enterprise Environments,” National Security Agency / Cybersecurity and Infrastructure Security Agency, Jan. 2021. [Online]. Available: https://media.defense.gov/2021/Jan/14/2002564889/-1/-1/0/CSI_ADOPTING_ENCRYPTED_DNS_U_OO_102904_21.PDF
[14] “Canary domain – use-application-dns.net,” Mozilla Support. [Online]. Available: https://support.mozilla.org/en-US/kb/canary-domain-use-application-dnsnet
[15] “Encrypted DNS Traffic Analysis and Classification,” IEEE Access, vol. 11, 2023. [Online]. Available: https://ieeexplore.ieee.org/document/10165086/
[16] S. Siby, M. Juarez, C. Diaz, N. Vallina-Rodriguez, and C. Troncoso, “Encrypted DNS -> Privacy? A Traffic Analysis Perspective,” in Proc. Network and Distributed Systems Security Symposium (NDSS), 2020. [Online]. Available: https://arxiv.org/abs/1906.09682
[17] “Darktrace Detection of State-Linked ShadowPad Malware,” Darktrace Blog, 2024. [Online]. Available: https://www.darktrace.com/blog/darktrace-detection-of-state-linked-shadowpad-malware
[18] “DNS Threat Landscape 2025,” Help Net Security, Aug. 2025. [Online]. Available: https://www.helpnetsecurity.com/2025/08/12/dns-threat-landscape-2025/
[19] “DNS over HTTPS: 3 Strategies for Enterprise Security Monitoring,” Carnegie Mellon University Software Engineering Institute. [Online]. Available: https://www.sei.cmu.edu/blog/dns-over-https-3-strategies-for-enterprise-security-monitoring/
[20] “Zero Trust DNS is Here: Elevating Enterprise Security on Windows 11,” Microsoft Tech Community, Feb. 2025. [Online]. Available: https://techcommunity.microsoft.com/blog/networkingblog/zero-trust-dns-is-here-elevating-enterprise-security-on-windows-11/4468743
[21] “Deploying Zero Trust DNS,” Microsoft Learn. [Online]. Available: https://learn.microsoft.com/en-us/windows/security/operating-system-security/network-security/zero-trust-dns/deploying-zero-trust-dns

Leave a Reply
You must be logged in to post a comment.