WHY TARGET EXCHANGE SERVER?
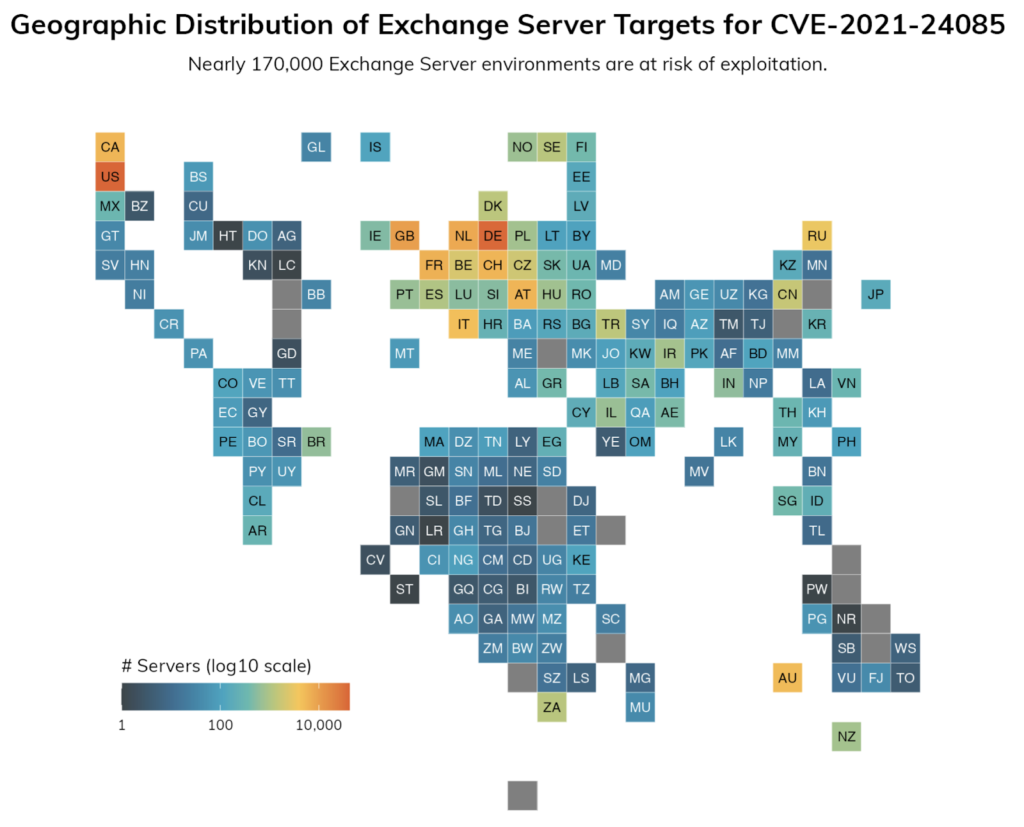
Out of endless amounts of public targets, e-mail servers serve a promising choice for several reasons. For the most part, mail servers always keep confidential secrets. Especially Exchange Server is the most well-known mail solution for enterprises and governments worldwide. Also have public mail servers been the target for Nation-sponsored hackers for a long time already. More than 400,000 Exchange servers exposed on the Internet [R16]. This also includes the assumption that all the data in the servers are stored unencrypted. The question arises on why an end-to-end encryption has been avoided all this time.
HAFNIUM
The attacks on Exchange Server were apparently started by a Chinese hacker group called Hafnium, which is said to have direct links with the Chinese government [R2]. The main intention of Hafnium seemed to tap into information primarily in the USA. The group aimed at a number of industries including infectious disease researchers, law firms, higher education institutions, defense companies, policy think tanks, and NGOs. As Hafnium is based in China it conducts its operations primarily from leased virtual private servers (VPS) in the United States [R2].
In their report Microsoft states that prior to the Exchange Server attacks, Hafnium already compromised victims by exploiting security flaws in internet-connected servers and by using legitimate open source frameworks such as Covenant. The group aims to gain access to a victim network where then they filter data on file sharing sites like MEGA [R3]
Additionally, in campaigns unrelated to these vulnerabilities, Microsoft has observed HAFNIUM interacting with the victim’s Office 365 tenants. While they often fail to compromise customer accounts, this intelligence activity helps the adversary to identify more details about the surroundings of their targets [R3].
SEQUENCE OF EVENTS
January 3 2021: Cyber espionage operations against Microsoft Exchange Server begin using the Server-Side Request Forgery (SSRF) vulnerability CVE-2021-26855
January 5: Initial report to Microsoft of the four flaws by a principal security researcher for security testing firm DEVCORE.
January 6: Identification of the attacks on the previously discovered flaws by Volexity
Mach 2: Microsoft releases emergency security updates to plug the four zero-day flaws in Exchange version 2013-2019 to counter the Hafnium attack.
March 3: The CISS issues an emergency directive for all federal agencies to disconnect from Microsoft Exchange on-premises servers and begin incident response procedures – Tens of thousands of Exchange servers have already been compromised worldwide, with thousands more servers getting freshly hacked each hour
March 5-8: Microsoft assumes further attacks by actors beyond Hafnium, targeting the same vulnerabilities the Chinese group exploited.
March 9: (“Patch Tuesday” ) Original publish date for the security updates ➔ Patch of 82 security holes in Windows and other software, including a zero-day vulnerability in its web browser software.
March 10: At least 10 “advanced persistent threat” (APT) cybercrime and espionage groups have been exploiting the Exchange flaws for their own purposes.
March 13: The CISA adds seven Malware Analyst Reports to identify web shells associated with Exchange vulnerabilities.
March 15: Microsoft releases a “one-click” On-Premises Mitigation Tool to assist customers who do not have dedicated IT security to apply updates to Exchange Server.
March 18: Microsoft announces their Defender Antivirus and System Center Endpoint Protection now automatically mitigates CVE-2021-26855 on any vulnerable server.
March 31: CISA releases supplemental direction on Emergency Directive for Exchange Server Vulnerabilities.
April 13: The FBI is granted a search and seizure warrant by a Texas court that allows the agency to copy and remove web shells from hundreds of on-premises Microsoft Exchange servers owned by private organizations.
Considering that the state has to aid in fixing those security issues shows how dramatic the situation and how underdeveloped many company infrastructures are in regards to such incidents.
See: [R11][R12]

Leave a Reply
You must be logged in to post a comment.