Category: System Designs
Usability and Security
Usability and Security – Is a tradeoff necessary? Usability is one of the main reasons for a successful software with user interaction. But often it is worsened by high security standards. Furthermore many use cases need authentication, authorisation and system access where high damage is risked when security possibilities get reduced. In this article the…
Security in Smart Cities
Today cities are growing bigger and faster than ever before. This results in various negative aspects for the citizens such as increased traffic, pollution, crime and cost of living, just to name a few. Governments and city administrations and authorities are in need to find solutions in order to alleviate these drawbacks. Over the past…
Differential Privacy – Privacy-preserving data analysis
It is widely known that tech companies, like Apple or Google and their partners collect and analyse an increasing amount of information. This includes information about the person itself, their interaction and their communication. It happens because of seemingly good motives such as: Recommendation services: e.g. word suggestions on smartphone keyboard Customizing a product or…
Beyond Corp – Google’s approach to enterprise security
What is Beyond Corp? Beyond corp is a concept which was developed and is used by Google and is by now adopted by some other companies. The idea behind it was to get away from the intranet and its perimeter defense, where, if you breach the perimeter you can access much of the enterprise data.…
Disaster prevention in Germany
This article has two main topics: First a short overview about the organization of the disaster prevention in Germany. The second part of this article is about the consequences of a national blackout and how to prepare for this disaster.
Server “less” Computing vs. Security
Summary about Serverless Computing with Security aspects.
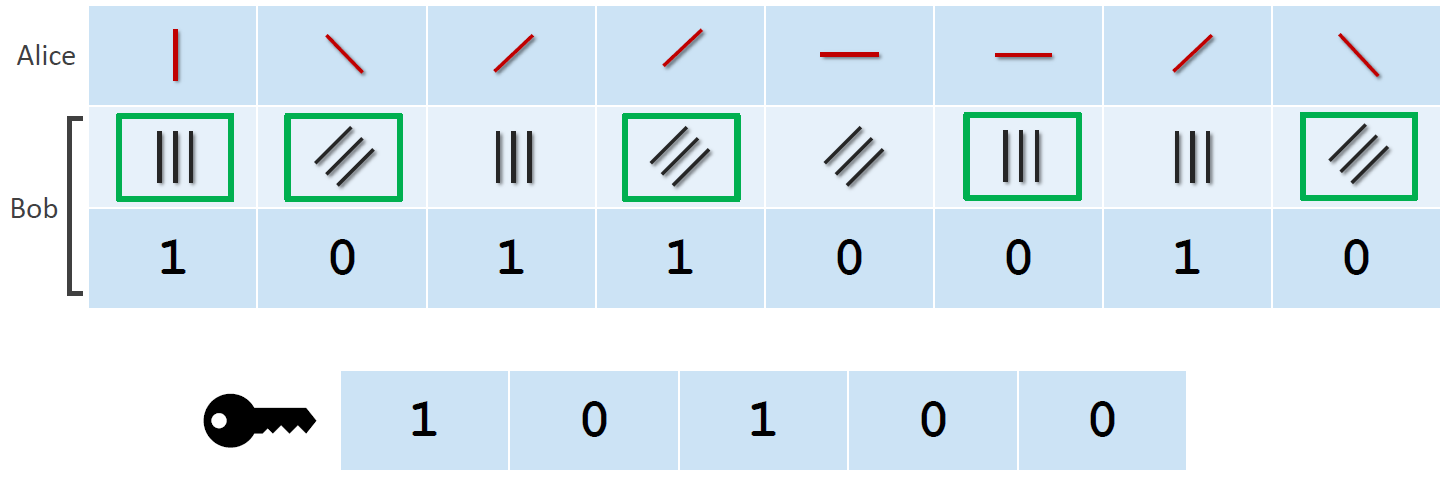
Quantum and Post-Quantum Cryptography
In a world where political activists and dissidents get persecuted by authoritarian governments, strong cryptography is more necessary than ever. But the general public benefits from it as well. Identity theft, banking fraud and cyber bullying can happen to anybody. The most effective protection is to not make sensitive material available to anybody. Unfortunately some…
- Cloud Technologies, Scalable Systems, Student Projects, System Architecture, Ultra Large Scale Systems
Building a fully scalable architecture with AWS
What I learned in building the StateOfVeganism ? By now, we all know that news and media shape our viewson these discussed topics. Of course, this is different from person to person. Some might be influenced a little more than others, but there always is some opinion communicated. Considering this, it would be really interesting…

You must be logged in to post a comment.