Tag: Linux
 Allgemein, Artificial Intelligence, ChatGPT and Language Models, Cloud Technologies, DevOps, Internet of Things, Scalable Systems, Student Projects
Allgemein, Artificial Intelligence, ChatGPT and Language Models, Cloud Technologies, DevOps, Internet of Things, Scalable Systems, Student ProjectsWelcome to the Future of Government Tech – Meet GuppyAI!
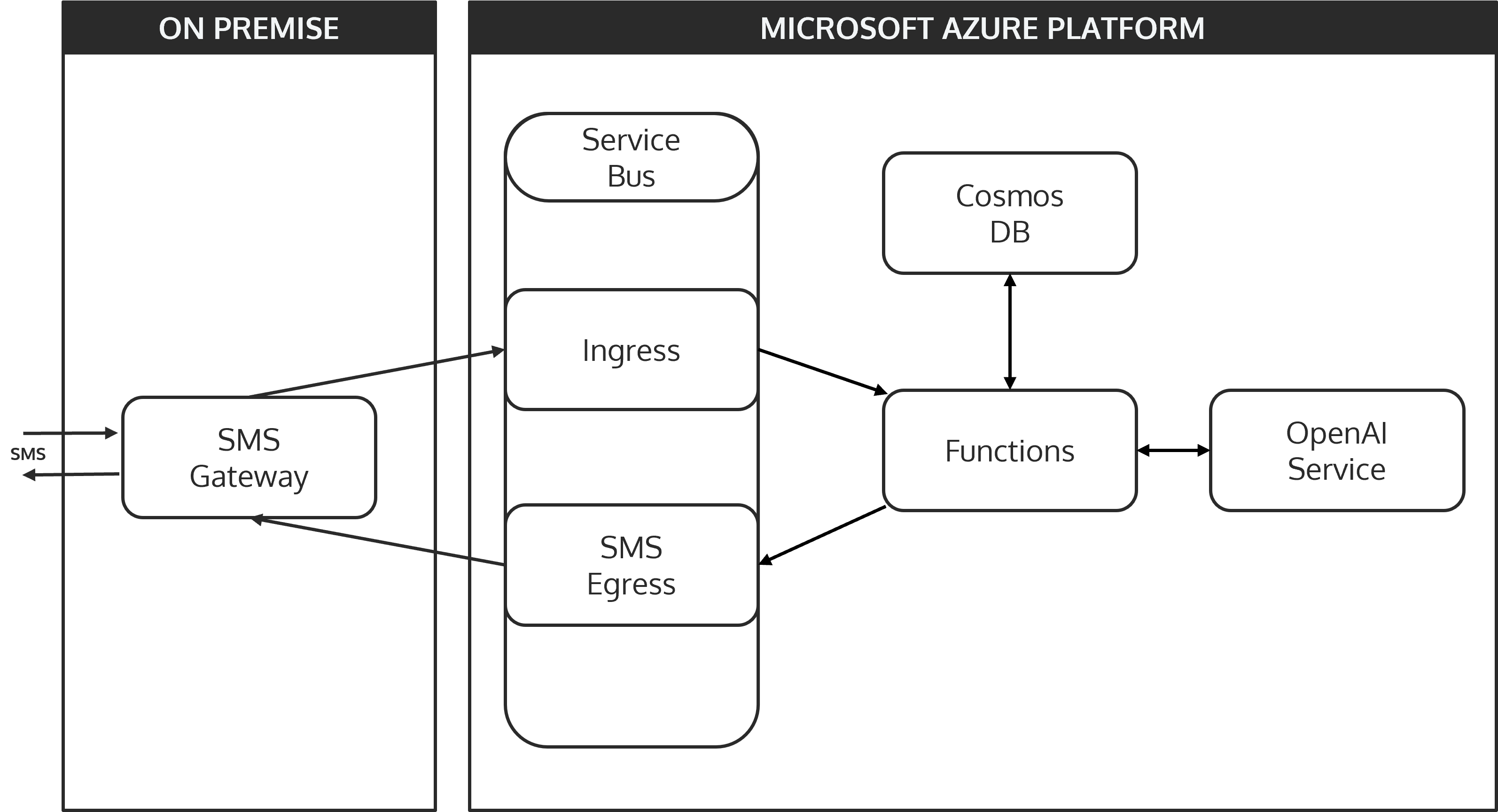
Read about our journey of developing GuppyAI, a friendly, SMS-powered AI chatbot designed to upgrade your skills without the hassle.
Improve your storage I/O performance today
an article by Lucas Crämer and Jannik Smidt DISCLAIMER This post tries to keep the complexity manageable while making a point clear. We are not systems engineers/kernel developers, so feel free to point out any mistakes/misunderstandings. This post probably does not present anything new for people who are working in systems engineering and/or kernel development.
KISS, DRY ‘n SOLID — Yet another Kubernetes System built with Ansible and observed with Metrics Server on arm64
This blog post shows how a plain Kubernetes cluster is automatically created and configured on three arm64 devices using an orchestration tool called Ansible. The main focus relies on Ansible; other components that set up and configure the cluster are Docker, Kubernetes, Helm, NGINX, Metrics Server and Kubernetes Dashboard. Individual steps are covered more or
Behind the scenes of modern operating systems — Security through isolation (Part 1)
In recent years, since the Internet has become available to almost anyone, application and runtime security is important more than ever. Be it an (unknown) application you download and run from the Internet or some server application you expose to the Internet, it’s almost certainly a bad idea to run apps without any security restrictions
Livestreaming with libav* – Tutorial (Part 2)
If you want to create videos using FFmpeg there is a basic pipeline setup to go with. We will first take a short overview over this pipeline and then focus on each individual section.
Livestreaming with libav* – Tutorial (Part 1)
Lifestreaming is the real deal of video today, however there aren’t that many content creation tools to choose from. YouTube, Facebook and Twitter are pushing hard to enable their users to stream vlogging-style content live from their phones with proprietary Apps, and OBS is used for Let’s Plays and Twitch streams. But when you want to stream
Exploring Docker Security – Part 2: Container flaws
Now that we’ve understood the basics, this second part will cover the most relevant container threats, their possible impact as well as existent countermeasures. Beyond that, a short overview of the most important sources for container threats will be provided. I’m pretty sure you’re not counting on most of them. Want to know more?
Exploring Docker Security – Part 1: The whale’s anatomy
When it comes to Docker, most of us immediately start thinking of current trends like Microservices, DevOps, fast deployment, or scalability. Without a doubt, Docker seems to hit the road towards establishing itself as the de-facto standard for lightweight application containers, shipping not only with lots of features and tools, but also great usability. However, another important topic is neglected very
Defense in Depth: a present time example
In this post, we want to take a look on the concept of defense in depth. Therefore we are going to examine Chrome OS, the niche operation system for web users.
