Tag: security
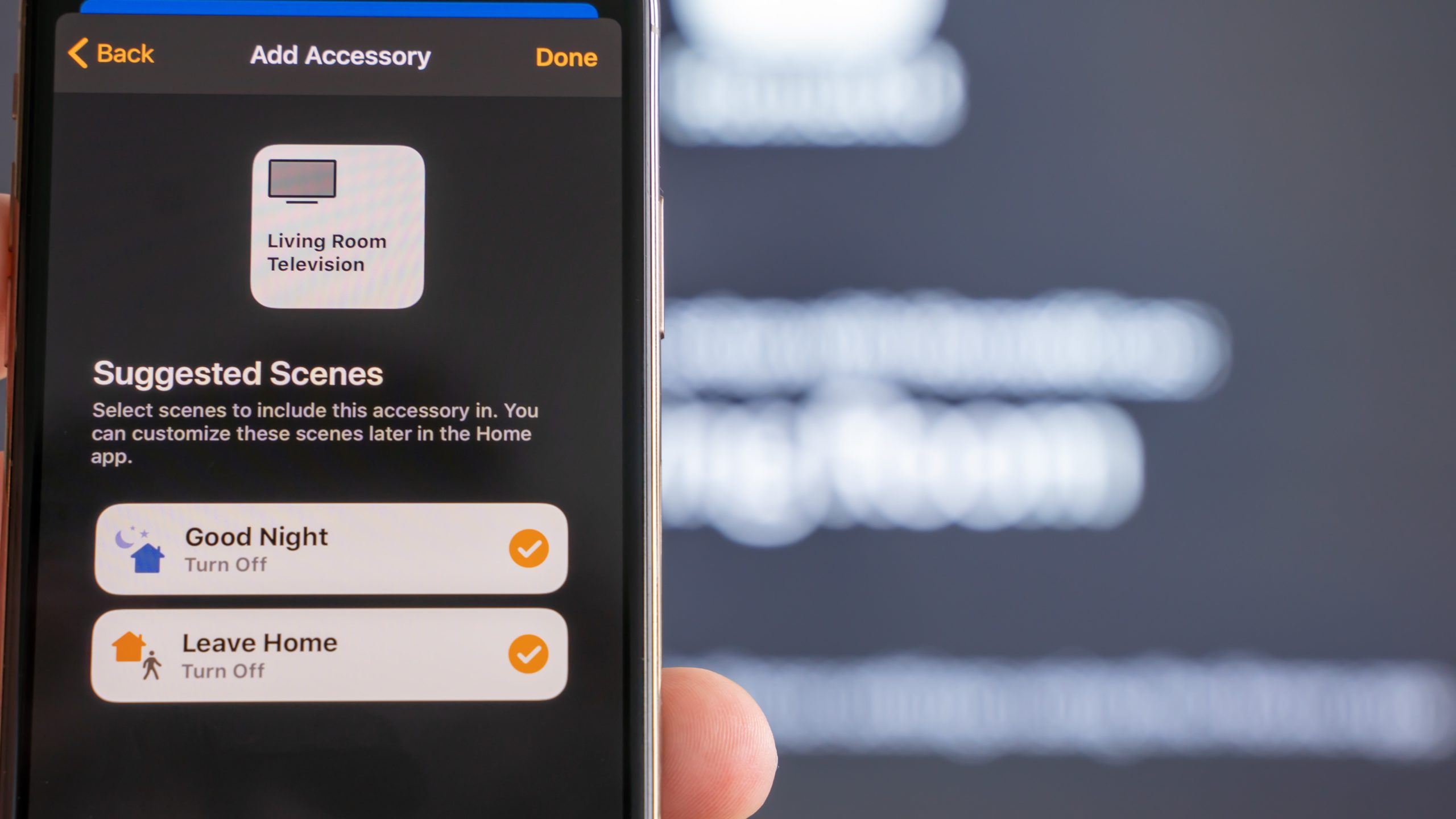
Why It’s So Easy to Hack Your Smart Home
Every day, new smart home accessories go online for the first time to join the Internet of Things. Many of them enjoy the unwarranted trust of their owners.
Supply Chain Attacks – Die Lieferkette schlägt zurück
ein Artikel von Verena Eichinger, Amelie Kassner und Elisa Zeller Nach SolarWinds schafft es eine neue Schlagzeile aus der IT-Welt in den Massenmedien ihre Kreise zu ziehen. Über 500 Supermärkte in Schweden mussten wegen eines Cyberangriffs schließen. Wie bereits bei SolarWinds handelt es sich auch hier um eine Supply Chain Attack (SCA). Mittlerweile fällt dieser
Zero Trust Security – The further development of perimeter security?
Most companies use perimeter security to secure their cooperate applications, services and data from attackers and unauthorised users. This approach includes a cooperate network, where clients, that are part of the network are able to access the applications. This includes attackers that got access to these networks.Additionally more applications are getting shifted from cooperate networks
Sicherheitssysteme in der Raumfahrt
Disclaimer Die heutige Raumfahrt oder auch allgemein Raumfahrt ist ein sehr komplexes und vielschichtiges Thema. Nicht grundlos werden umgangssprachlich schwierige Themen als “Raketenwissenschaften” bezeichnet. Dieser Artikel möchte nicht die Raumfahrt in ihrer Gänze beschreiben sondern nur einen sehr kleinen Teil im Bereich der Sicherheit beleuchten. Hierfür wurden sich vor allem auf den Start einer Rakete
Behind the scenes of modern operating systems — Security through isolation (Part 1)
In recent years, since the Internet has become available to almost anyone, application and runtime security is important more than ever. Be it an (unknown) application you download and run from the Internet or some server application you expose to the Internet, it’s almost certainly a bad idea to run apps without any security restrictions
Corona Warning App
In 2020 many things are different. People work and study from home, wear face masks and are facing restrictions in their fundamental rights. These measures and restrictions were taken to bring the global pandemic under control. More than 800.000 people have died as a result of Covid-19 (SARS-CoV-2) (25.08.2020). “Let’s build an app for it”
GDPR and Information Security: A practical guide for Startups and small businesses
Let me start with a story. My first contact with GDPR (general data protection regulation) and the topic of information security was during my bachelor throughout an app project. We had set ourselves the goal of uploading the app to Google Play Store by the end of the semester and were thus inevitably confronted with
IoT security – The current situation, “best practices” and how these should be applied
Smart thermostats, lamps, sockets, and many other devices are no longer part of any futuristic movies. These items can be found in most households, at least in parts, whether in Europe, America, or Asia. A trend that affects the entire globe and is currently gaining ground, especially in industrialized countries. It seems to be obvious…
How does Tor work?
Written by Tim Tenckhoff – tt031 | Computer Science and Media 1. Introduction The mysterious dark part of the internet – hidden in depths of the world wide web, is well known as a lawless space for shady online drug deals or other criminal activities. But in times of continuous tracking on the Internet, personalized

About the Robustness of Machine Learning
In the past couple of years research in the field of machine learning (ML) has made huge progress which resulted in applications like automated translation, practical speech recognition for smart assistants, useful robots, self-driving cars and lots of others. But so far we only have reached the point where ML works, but may easily be

You must be logged in to post a comment.